Most security risks in Microsoft 365 are not caused by missing features, but by misconfiguration, over-permissioning, and lack of visibility.
From privileged access to Conditional Access design, understanding how identity is used across your environment is critical to reducing risk.

Control privileged access before it becomes a risk
Review and secure administrative access across your tenant, ensuring least privilege, proper role assignment, and effective use of tools such as PIM.
- dentify and reduce standing privileged roles (Global Admin, Privileged Role Admin, etc.)
- Implement just-in-time access using Privileged Identity Management (PIM)
- Remove legacy or “temporary” admin access that has become permanent
- Introduce approval workflows and access reviews for high-impact roles
- Align admin access with Zero Trust principles (no implicit trust)

Design Conditional Access with intent
Move beyond default policies and design Conditional Access aligned to your organisation’s risk profile, device posture, and user behaviour.
- Replace legacy VPN/RDP approaches with secure modern access
- Align device, identity, and access controls into a unified model
- Support hybrid, remote, and frontline workforce scenarios
- Improve user experience without compromising security
- Provide visibility and control across all endpoints
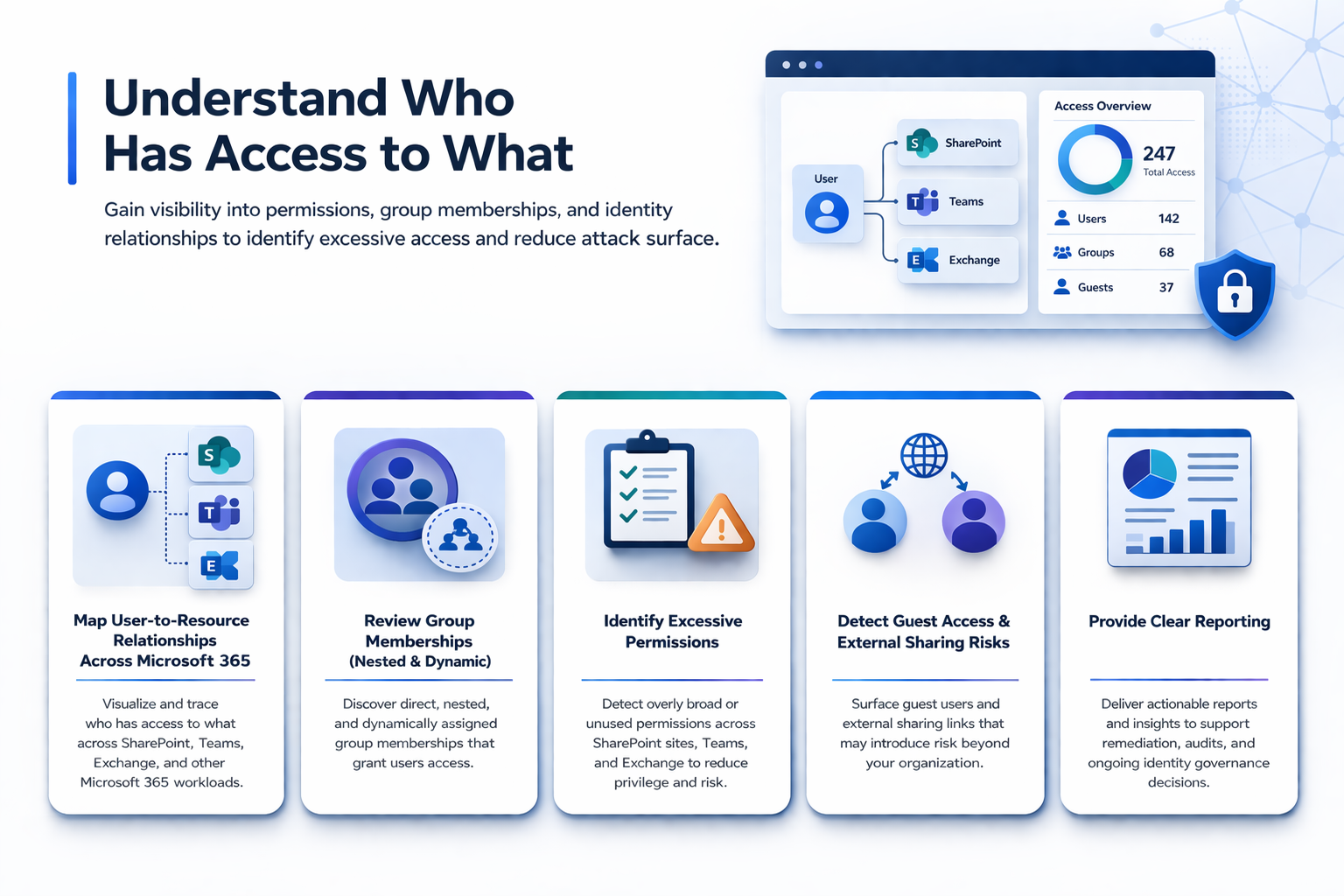
Understand who has access to what
Gain visibility into permissions, group memberships, and identity relationships to identify excessive access and reduce attack surface.
- Map user-to-resource relationships across Microsoft 365
- Review group memberships (including nested and dynamic groups)
- Identify excessive permissions across SharePoint, Teams, and Exchange
- Detect guest access and external sharing risks
- Provide clear reporting to support remediation and governance decisions
